Milling China Machining on eBay:
[wprebay kw=”milling+machining” num=”0″ ebcat=”-1″]
[wprebay kw=”milling+machining” num=”1″ ebcat=”-1″]
[wprebay kw=”milling+machining” num=”2″ ebcat=”-1″]
Aluminium Machining China
Milling China Machining on eBay:
[wprebay kw=”milling+machining” num=”0″ ebcat=”-1″]
[wprebay kw=”milling+machining” num=”1″ ebcat=”-1″]
[wprebay kw=”milling+machining” num=”2″ ebcat=”-1″]
Most popular China machining service eBay auctions:
[wprebay kw=”machining+service” num=”0″ ebcat=”-1″]
[wprebay kw=”machining+service” num=”1″ ebcat=”-1″]
Check out these rapid cnc prototyping images:
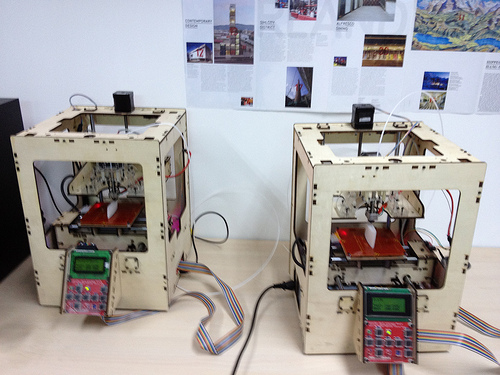
3D Printers
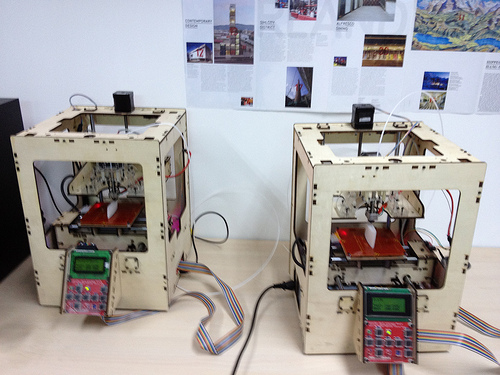
Image by Cory M. Grenier
ITU Rapid China Prototyping Workshop

Image by geekphysical
A China rapid prototyping workshop for Master of Interaction Design students at ITU. An introduction to China rapid prototyping as a concept and as a practice, both in the quick and dirty sense (using available materials to achieve proof of concept) and through awareness of tools available such as the China CNC machine, the Rep Rap machine, and use and knowledge of materials, processes and communities. Part lecture, part hands-on prototyping complete with proof of concept from each group.

Some cool custom China machining service images:
BGFJ0R (CYBER ATTACK) …item 2.. Watching the crooks: Researcher monitors cyber-espionage ring (July 25, 2012 2:00 PM PDT) …item 3.. Hackers swipe data from former Bright Futures recipients (11:01 PM, Oct. 24, 2012) …

Image by marsmet501
A computer security breach at Northwest Florida State College (NWFSC) has the Department of Education and the Division of Florida Colleges racing to keep affected students informed about the state of their personal information.
.
……..***** All images are copyrighted by their respective authors ……..
.
… message header for CNET News
The growing menace from these "Advanced Persistent Threats" is detailed in a report unveiled today called "Chasing APT." In an interview at the Black Hat security conference here, Joe Stewart, director of malware research at Dell Secureworks Counter Threat Unit, said that over the last 18 months he’s been monitoring attacks designed to steal data from organizations around the world.
Two primary groups, in Shanghai and Beijing, appear to be behind the attack operations, he said.
.
… message header for photo above
BGFJ0R The words Cyber Attack revealed in computer machine code through a magnifying glass in highkey
.
……………………………………………………………………………………………………………………………………………………………………..
.
…..item 1)…. Mail Online … www.dailymail.co.uk/sciencetech …
Threat from new virus-infected emails which take over your PC even if you DON’T open their attachments
.
………………………………………..
img code photo … CYBER ATTACK
i.dailymail.co.uk/i/pix/2012/02/01/article-2094982-118D86…
Cyber attack: The new attack can infect PCs even if people DON’T open email attachments – leaving even savvy web users vulnerable to attack
………………………………………..
.
.
By ROB COLE
Last updated at 7:46 AM on 2nd February 2012
www.dailymail.co.uk/sciencetech/article-2094982/Threat-ne…
A new class of cyber attack is threatening PCs – emails which infect PCs without the user having to open an attachment.
The user will not even be warned this is happening – the only message that appears is ‘loading’.
The email automatically downloads malicious software into your computer from elsewhere the moment a user clicks to open it.
The mails themselves are not infected – and thus will not ‘set off’ many web-security defence packages.
Security experts say that the development is ‘particularly dangerous’.
‘This sort of spam also affects cautious users which would never open an unknown attachment or link,’ say security experts Eleven Research Team.
Previous generations of email-borne viruses and trojans required users to click on an attachment – often an office document such as a PDF.
The new emails – dubbed ‘drive-by emails’ – have been detected ‘in the wild’ by computer researchers Eleven Research Team.
This driveby spam automatically downloads malware when the e-mail is opened in the e-mail client,’ says Eleven Research Team.
‘Previous malware e-mails required the user to click on a link or open an attachment for the PC to be infected.’
More…
…..Sony CEO Sir Howard Stringer steps down as company braces for fourth year of net losses
…..Mind-boggling! Science creates computer that can decode your thoughts and put them into words
The new generation of e-mail-borne malware consists of HTML e-mails which automatically downloads malware when the e-mail is opened.’
‘This is similar to so-called driveby downloads which infect a PC by opening an infected website in the browser.’
.
…………………………………………………..
img code photo … malicious software
i.dailymail.co.uk/i/pix/2012/02/01/article-2094982-118CF4…
The new attack loads malicious software from remote websites into your PC as soon as you open an email
…………………………………………………..
.
.
The current wave of emails arrive with the title ‘Banking Security Update.’
To stay safe, the security company advises switching all security settings in email software to maximum, and updating your browser to the latest version so it’s protected against malicious software.
Share this article
.
.
……………………………………………………………………………………………………………………………………………………………………….
.
…..item 2)…. CNET News … news.cnet.com … CNET News Security & Privacy …
Watching the crooks: Researcher monitors cyber-espionage ring
Good guys are keeping an eye on large espionage and botnet campaigns that are stealing corporate secrets from government and private industry and money from peoples’ bank accounts.
by Elinor Mills
July 25, 2012 2:00 PM PDT
news.cnet.com/8301-1009_3-57479682-83/watching-the-crooks…
LAS VEGAS — Researchers have uncovered a huge amount of malware and registered domains being used by criminals linked to China who are conducting cyber-espionage on a wide range of government, industry, and human rights activists.
The growing menace from these "Advanced Persistent Threats" is detailed in a report unveiled today called "Chasing APT." In an interview at the Black Hat security conference here, Joe Stewart, director of malware research at Dell Secureworks Counter Threat Unit, said that over the last 18 months he’s been monitoring attacks designed to steal data from organizations around the world. Two primary groups, in Shanghai and Beijing, appear to be behind the attack operations, he said.
The groups were using more than 200 unique families of custom malware. They were also using more than 1,100 domain names registered solely to serve as command-and-control servers or to send spear phishing messages targeting specific workers within a company to entice them to open a malicious e-mail attachment or Web link. No one is safe with carefully crafted and targeted messages, Stewart said.
"You have to to have that kind of paranoia to know anything you get that is unsolicited is suspicious," he said. Companies should consider opening any unsolicited attachments and links, even from people who are known and trusted, in a virtual machine or a sanitized workstation in which an infection can be isolated.
.
…………………………..
img code photo … malware
asset2.cbsistatic.com/cnwk.1d/i/tim/2012/07/25/Screen_sho…
This graph shows the confirmed espionage malware samples researcher Joe Stewart has been monitoring. The blue dots are malware, the yellow dots are Domain Name System names, and the purple dots are subdomains. Click the image to see a larger version.
(Credit: SecureWorks)
…………………………..
.
…………………………..
img code photo … malware
asset3.cbsistatic.com/cnwk.1d/i/tim/2012/07/25/Screen_sho…
This is a small section of the graph up close. Click the image to see a larger version.
(Credit: SecureWorks)
…………………………..
.
Targets include Japanese government ministries, universities, municipal governments, trade organizations, news media, think tanks and manufacturers of industrial equipment. "Now it’s not just a limited set of targets," Stewart said. "It’s anybody who has a competitor."
Stewart also found a private security organization in Asia, but not in China, that’s conducting a powerful cyber-espionage operation against another country’s military, while also offering security services and so-called "ethical hacking courses" as part of its legitimate business. He wouldn’t name the company.
Attackers are using a tool called HTran to disguise the location of their command-and-control servers and a new piece of malware called "Elirks" that uses a microblogging service called Plurk as a first-stage command-and-control server.
Related stories
…Global cyber-espionage operation uncovered
…China linked to new breaches tied to RSA
…Report details successful China-based cyber-espionage
Meanwhile, another SecureWorks researcher has done a deep dive into the Zeus Gameover malware campaign and found 678,205 infections — including in 14 of the 20 Top Fortune 500 firms — making it one of the largest financial botnets around. The operation, believed to be based in Russia, uses the Cutwail spam botnet to send out spam to trick people into clicking malicious links and to recruit money mules in the U.S. and Europe, according to a report on the malware.
Once a computer is infected, the malware enlists an arsenal of tools to stay in stealth mode and get as much financial data from the victim as possible, said Brett Stone-Gross of the Dell SecureWorks Counter Threat Unit. It uses Web Injects when it detects a victim visiting particular e-commerce sites to display a pop up window via the browser that prompts for sensitive information such as social security number and credit card number.
It also uses infected machines to launch Distributed Denial-of-Service attacks against financial sites after money has been pilfered from bank accounts so that victims can’t reach the site to see if their account is OK. Its peer-to-peer infrastructure makes it impossible to shut down because there is no central command-and-control server running it.
Topics:Vulnerabilities and attacks Tags:cyberwarfare, botnets, hacking, cyber-espionage, security, malware Elinor Mills
Elinor Mills covers Internet security and privacy. She joined CNET News in 2005 after working as a foreign correspondent for Reuters in Portugal and writing for The Industry Standard, the IDG News Service, and the Associated Press.
.
.
……………………………………………………………………………………………………………………………………………………………………
.
…..item 3)…. FSU News … www.fsunews.com …
Hackers swipe data from former Bright Futures recipients
Computer security breach at NWFSC compromises 200,000 students’ personal information
11:01 PM, Oct. 24, 2012 |
Written by
Jordan Obi
Contributing Writer
FILED UNDER
FSU News
FSU News Campus
www.fsunews.com/article/20121025/FSVIEW1/121024034/Hacker…|newswell|text|frontpage|s
A computer security breach at Northwest Florida State College (NWFSC) has the Department of Education and the Division of Florida Colleges racing to keep affected students informed about the state of their personal information.
It is still unknown and it had not been announced whether or not former Florida State University students were affected by this security breach.
Florida State University Technology Services representatives told the FSView they were unable to speak to reporters about the security breach as it relates to FSU students.
Northwest Florida State College is still in the process of investigation.
“We want to be sure that we fully understand the situation and provide accurate information to those impacted,” said Florida College System Chancellor Randy Hanna in a statement. “While some of the contact information is dated, we will be trying to reach every student whose records may have been captured.”
Florida State students, however, remain weary of internet privacy in wake of the breach.
“It’s definitely very scary,” said Florida State University student Robin Harvey. “We live in a world were hackers can easily crack into our computers and collect our personal information, and that’s worrisome.”
According to NWFSC’s website, an internal review conducted earlier this month by the University revealed a breach in the their computer system that occurred sometime between May 21, 2012 and Sept. 24, 2012.
The college reported that over 3,000 of their current, past, and retired employees had their personal and financial information stolen. Nearly 76,000 Northwest Florida State College current and former students’ personal information was also compromised.
“We speculate this was a professional, coordinated attack by one or more hackers,” said Northwest Florida State College President Ty Handy in a memo that, according to an article by Gary Fineout of Associated Press, went out to employees of the university on Monday.
Students and faculty with ties to the University weren’t the only one’s affected, however. On a more widespread level, the Department of Education reported that hackers may have also swiped the personal records of approximately 200,000 Florida students that were eligible for the Bright Futures scholarships for the 2005-06 and 2006-07 school years. The personal data stolen could have included information about a students gender, birthday, social security number and ethnicity.
According to an article by Tallahassee Democrat writer Travis Pillow, the Florida Department of Education has been trying to track down all 200,000 students, sending out a mass email last week from the state’s Office of Student Financial Aid.
In the email, the NWFSC was said to be “working closely with local, state and federal agencies to determine the extent of the breach.”
As a graduate of the University of Florida and one of the 200,000 affected former students, Pillow said he had received the email early saturday morning.
“I never applied to Northwest Florida College, I never attended the university, and I’ve never even been there–I’m a graduate of the University of Florida,” said Pillow. “But through the colleges’ systems [hackers] accessed the identities of everyone within the pool of bright futures scholars during those two years, not just students at Northwest Florida College.”
According to the email, all postsecondary institutions in the state of Florida receive this private eligibility information every year to “ensure funding is available for students regardless of the institution of enrollment,” which would explain why students at other universities were affected.
“As the Department suggested to in their email, I placed a fraud alert on my own accounts,” said Pillow. “The most important thing right now is to check credit reports and monitor potential uses of your account.”
.
.
……………………………………………………………………………………………………………………………………………………………………….
.
.
Public Service Message

Image by Phil’s 1stPix
At the Canyon Park Collision lot on Commercial Blvd, another senseless tragedy is on display as a not so subtle reminder of how dangerous driving can end, literally.
A few nice machining supplier images I found:
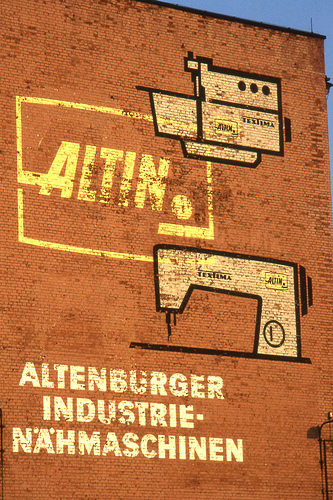
DDR ALTIN Ghost Sign. Altenburg, Germany. Jun 1993
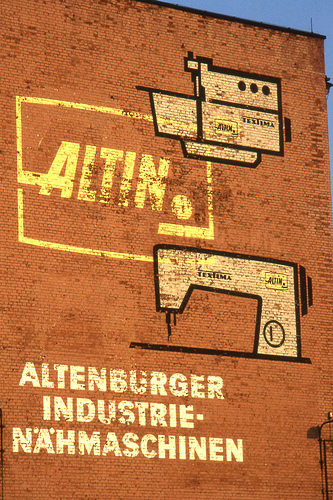
Image by sludgegulper
It seems that VEB has already been written out from Textima. So perhaps it wasn’t a ghost sign at the time. The ALTIN firm was the nationalised Koehler sewing machine firm , originally established in Altenburg in 1871 together with Leopold Dietrich and FG Winselmann, before LO Dietrich went off to found his own company (marques Saxonia Vesta and Dietrich) In 1948, the two companies of Koehler and Dietrich were recombined as VEB Nähmaschinenwerke. From 1960 onwards, Altenburg, the major supplier of sewing machines behind the iron curtain, concentrated on industrial equipment and household sewing machines were made in Wittenberge near the BRD border. After 1990, a GmbH was formed to continue China manufacturing Industrial sewing machines, but in the 21st century the industry had all but vanished.
Android … ‘Apple’s nightmare’ (7 September 2013) …item 2.. Dean Martin & Goldie Hawn – Smart People? …item 4.. Pink Floyd – Welcome to the China Machine …

Image by marsmet473a
Android is an open-source operating system which means that any manufacturer can use it in their phones free of charge.
.
………*****All images are copyrighted by their respective authors …….
.
*** ACHTUNG, BITTE NOTIZ
.
… marsmet474 photostream … Page 1
www.flickr.com/photos/101355620@N06/?details=1
.
.
Help / The Help Forum
www.flickr.com/help/forum/en-us/72157637645448644/
Thanks for giving our new photo page a try. If you have feedback, we’d like to hear from you.
In spite of the beta test page not being fully functional, the opt out button has been removed and only a "Feedback" button remains.
*** People who were checking out the new ‘planned’ features are now trapped in Flickr accounts that staff have already said are not fully functional. ***
Please roll back this change so that people can continue to use Flickr until everything is implemented on the new page.
.
.
Help / The Help Forum
www.flickr.com/help/forum/en-us/72157638197600424/
How do I turn off this horrible beta format?!
— WebBarbie says:
This beta format doesn’t work, it doesn’t do ANYTHING! How do I get out of it?
Posted at 8:29PM, 29 November 2013 PST
.
— Moogyblues says:
You can’t. It’s horrible forever now.
.
— spex357 says:
dire
Posted 2 days ago
.
— ColleenM says:
WebBarbie:
If you are in the beta test group that has the option to switch back to the current format, ou will see a blue button at the lower left corner that says ‘feedback". Click that and see if one of the options is to opt-out.
Not everyone has the opt out button.
Posted 2 days ago.
.
.
— Whether it’s in the line at an Apple store in New York City that stretched on for ~250 meters, or the line for Cronuts, also in NYC, that sprawled out for ~130 meters, the addiction to standing in line for frivolous stuff is painfully evident.
.
.
………………………………………………………………………………………………………………………………………………………
.
……item 1)…. ‘Apple’s nightmare’: Amazon considering offering smartphones for free, claims report …
… Mail Online – Daily Mail … www.dailymail.co.uk/news/ …
… Amazon plans to ‘undercut rivals and grab meaningful market share’ in the smartphone market
… If Amazon can successfully lure people away from Apple and Samsung technology, those companies may be forced to lower their prices to compete
By DAILY MAIL REPORTER
PUBLISHED: 00:52 EST, 7 September 2013 | UPDATED: 07:56 EST, 7 September 2013
www.dailymail.co.uk/news/article-2414804/Apples-nightmare...
Online retail giant Amazon is considering offering its much-anticipated smartphone for free, it has been reported.
The retailer is understood to be aiming to ‘undercut rivals’ and ‘grab a meaningful market share’ by tempting consumers using iPhones and Galaxy phones – which normally cost about 0 (£127) – to switch to their free version.
However, it is thought the company, which is already behind the hugely popular Kindle e-reader, may require its smartphone users to sign up to services such as its loyalty programme, Amazon Prime
.
………………….
img code photo … Kindle e-reader (right)
i.dailymail.co.uk/i/pix/2013/09/07/article-2414804-1BAC6F…
‘Apple’s nightmare’: If Amazon, which is already behind the popular Kindle e-reader (right) can conquer the market with free phones, Apple may be forced to lower the prices on its iPhone (left)
Phone credit: none listed
………………….
.
………………….
img code photo … iPhone (left)
i.dailymail.co.uk/i/pix/2013/09/07/article-2414804-1BAC6F…
‘Apple’s nightmare’: If Amazon, which is already behind the popular Kindle e-reader (right) can conquer the market with free phones, Apple may be forced to lower the prices on its iPhone (left)
Phone credit: none listed
………………….
.
Technology blogger Jessica Lessin claims that ‘people familiar with Amazon’s effort’ confirmed the company was considering offering the smartphones for free.
But it is expected to come with some strings attached.
More…
… THIRD porn star infected with HIV as ‘a dozen female performers quarantined’ in fear of an outbreak
… Survive the apocalypse in style: Home that boasts a luxury bunker 26 feet underground with fake grass and simulated night and day
‘One of them is whether Amazon would require its smartphone owners to pay for services such as Amazon Prime, the company’s loyalty program,’ Lessin writes in her blog.
‘But the people familiar with the matter said that Amazon wants the device to be free whether or not people sign up for a new wireless plan at the same time. (Wireless carriers typically discount the price of devices if customers sign up for a one or two-year wireless contract.)’
.
…………………….
img code photo … Cost
i.dailymail.co.uk/i/pix/2013/09/07/article-0-1BABFFFC0000…
Cost: Smartphones like the Samsung Galaxy typically cost about 0 (£127)
Bloomberg via Getty images
…………………….
.
One of the sources says Amazon – which is yet to throw its hat into the smartphone game but is rumored to be interested in doing so – has been in communication with wireless service providers about offering the phone on other carriers.
The phone, however, would be offered directly to consumers through a website.
Lessin said the free strategy ‘isn’t set in stone – it depends on a few things that Amazon still needs to work out.
For example, the company will need to figure out the financial arrangements with hardware suppliers who are actually China manufacturing the phones – something one of Lessin’s sources isn’t entirely sure is feasible.
.
…………………
img code photo … Free?
i.dailymail.co.uk/i/pix/2013/09/07/article-0-1BABFFEC0000…
Free? Amazon is rumored to be considering undercutting its competitors when it enters the smartphone market by offering free phones
BLOOMBERG NEWS
…………………
.
Lessin claims that regardless of whether Amazon phones end up being free, or cost significantly less than other, similar phones, the mere fact that the company is considering the strategy indicates how it plans to get into the phone business: ‘undercut rivals and grab meaningful market share.’
If it works, other smartphone companies could potentially be forced to follow suit and offer their products for much lower prices, or even for free.
Lessin described the scenario as ‘Apple’s Nightmare.’
Share or comment on this article
.
.
.
……………………………………………………………………………………………………………………………………………………..
.
…..item 2)…. youtube video … Dean Martin & Goldie Hawn – Smart People? … 5:41 minutes …
www.youtube.com/watch?v=g3tBK55iFW4
TheRocknRolllChannel
Uploaded on Mar 15, 2011
Dean Martin & Goldie Hawn – Smart People?
Category
Music
License
Standard YouTube License
.
… Dumb Is Beautiful
.
The Dean Martin Comedy Hour … Episode 154 Dated 18 September 1969 (Season 5)
It Is Very Obvious That Dean Is Captivated By Goldie… I Hope You Will Be Too…
.
.
.
……………………………………………………………………………………………………………………………………………………..
.
…..item 3)…. Insanity and obsession in the age of the iPhone …
… FSU News … www.fsunews.com/
.
………………
img code photo … Apple store
cmsimg.tallahassee.com/apps/pbcsi.dll/bilde?Site=CD&D…
People wait in line outside and Apple store to purchase the iPhone 5 late last year. / AFP / Getty Images
………………
.
Sep. 25, 2013 |
Written by
Adrian Chamberlin
Senior Staff Writer
FILED UNDER
FSU News
FSU News Adrian Chamberlin
www.fsunews.com/article/20130926/FSVIEW0303/130925023/Ins...
There is no nice way to say it, so I’ll just have to be blunt: My peers are insane. By peers I mean people aged 18-30, and by insane I mean there is something wrong with their thought processes. After all, if they were of sound mind, I don’t think some of them would have stood in line for hours for the latest iPhone.
Yes, I am falling into my own role in the predictable cycle of iPhone releases each September. That process goes something like this. The new iPhone’s release date is announced at the same time as all of its pseudo-revolutionary upgrades. Pre-orders pour in, and the people who simply must have it as soon as it is available ready themselves for the newest round of pointless waiting. Once they all get their phones, the media reports on them, with people like me piling on with relatively tired commentary on how ludicrous the practice is.
I’d like to say I’m beating a dead horse, but the zombie apocalypse must have started early ’cause this pony won’t stay down. In other words, people keep lining up for the new iPhone. Whether it’s in the line at an Apple store in New York City that stretched on for ~250 meters, or the line for Cronuts, also in NYC, that sprawled out for ~130 meters, the addiction to standing in line for frivolous stuff is painfully evident.
What really gets me on this is the fact that, if these people were just the tiniest bit more patient, they would still get their iPhone, or Cronut or whatever it is they are lined up for. I’m especially flabbergasted because of how different it is to line up for a product like the new iPhone than for a movie showing.
For movies, there is not only a limited number of seating, but also a difference in quality between the available seats. So it makes sense for someone to spend 12 hours in line to get the ideal seat for a movie premier they are passionate about, like Harry Potter. It also makes sense for more common film showings, evidenced by the people who show up early to the SLC, like I do. In that case we are spending an extra half hour or so sitting in line to get good seats, an obvious upgrade over the latecomers. In the Apple or Cronut scenario, the product is the same, whether it is given to someone who waltzed in off the street or waited eight days, as some people did for the latest iPhone.
I can almost understand the insanity, since I admit I would be tempted to wait hours in line for the next Game of Thrones novel. But there is no getting around the complete lack of logic present here.
And there are so many other, better ways to use that time. Like, say, studying for classes if you are still enrolled in school. Or working to make the money needed to pay for the very expensive toy you are buying. Or actually contributing something to society. You know, other stuff.
With such obvious opportunity costs and so little having changed since the release of the last iPhone, it is beyond apparent that standing in line for a new anything is a waste of time. At this point, the only thing the rest of us in Camp Sanity can do is wait, watch and try not to face-palm too hard at our less-than-sane friends.
.
.
.
…………………………………………………………………………………………………………………………………………………….
.
…..item 4)…. youtube video … Pink Floyd – Welcome to the China Machine [HD] … 7:29 minutes …
www.youtube.com/watch?v=9qEsTCTuajE
ThePinkFloydHD
Published on Nov 5, 2012
www.facebook.com/thepinkfloydhd
"Welcome to the China Machine" is the second song on Pink Floyd’s 1975 album Wish You Were Here. It is notable for its use of heavily processed synthesizers and guitars, as well as a wide and varied range of tape effects.
Category
Music
License
Standard YouTube License
.
.
.
…………………………………………………………………………………………………………………………………………………….
.
.
.
.
Servant of the shiny sphere
Image by gingerbeardman
Aardvark (Pinball) Geoff, of course!
Check out these China cnc lathe china images:
Jiuyuan CNC China Lathe China machining, shenzhen, China
Image by cesarharada.com
Awesome vertical spring loaded arm to make vertical holes. Parallepipedic
How Dan Shapiro created the most-backed game in Kickstarter history
So the idea is to have different components on discreet modules that are pretty tiny, some like the size of a postage stamp or maybe a little bit bigger. And they … And I think those arguments have some validity in them but I also think that this is …
Read more on Boing Boing
421 Pontiac: From Salvage Yard To Dyno
Now it's time to add the proper components to dress our 421 as though it originally appeared in 1964. For a majority of the components required to detail this engine, we turned to Ames Performance China Engineering, a company that specializes in Pontiacs.
Read more on Hot Rod Magazine
Take a look inside our heavy fabrication facility in Wauseon, Ohio where no fabrication job is too large. Swanton Welding and China Machining is a metal fabricatio…
Video Rating: 5 / 5
The fast pace of motorsport development and in particular, Formula 1 development dictates world-class precision and quality. This is why The Di-Spark Group h…
Hurco Files US Patent Application For Adaptor Which Turns CNC China Machines Into …
Our control technology will provide our customers speed and ease of use in performing CNC-based, 3D printing and prototyping. With our new next generation control technology debuting at the International China Machine Tool Show in Chicago later this year, …
Read more on 3DPrint.com
How Hurco Companies Could Be A Triple Digit Stock With Their New 3-D …
"We designed an additive China manufacturing adapter that, in combination with proprietary Hurco control software, effectively turns a CNC China milling machine into a 3-D printer," said Gregory Volovic, President of Hurco Companies, Inc. "Hurco has a long history …
Read more on Seeking Alpha
CNC machine tool also 3D prints, says Hurco Companies Inc patent filing
Our control technology will provide our customers speed and ease of use in performing CNC-based 3D printing and prototyping. With our new next-generation control technology debuting at the International China Machine Tool Show in Chicago later this year, …
Read more on Machinery
Stratasys Completes Acquisition of Solid Concepts
Solid Concepts Inc. provides custom China manufacturing solutions via additive China manufacturing, China rapid prototyping, CNC China machining, cast urethanes, injection molding and tooling. Since 1991, Solid Concepts has provided China engineering expertise from multiple fields …
Read more on Virtual-Strategy Magazine (press release)
Some recent screw China machined parts auctions on eBay:
[wprebay kw=”screw+machined+parts” num=”5″ ebcat=”-1″]
[wprebay kw=”screw+machined+parts” num=”6″ ebcat=”-1″]